EM12c Release 4, Private Roles
Until OEM11g, it was very common that all folks were either Super Administrators or Administrators and only a few shops took the time to create roles outside of these two essential roles. Super Administrator, (SA) was pretty straight forward- the SA had essentially the same access as the repository owner and should only be allocated to those that should have this deep access to the Enterprise Manager environment, but administrator access was more of a mystery. This was assigned to anyone who wasn’t considered for SA rights and we often called it good.
With Enterprise Manager 12c, there was a huger overhaul to the administrator assignment, along with multiple secondary roles, roles that accompanied plug-ins and now with Release 4, we have the addition of Private Roles.
With this change, where once a Super Administrator would have logged in as SYSMAN to manage jobs or manage credentials, you can now create private roles that allow one administrator to grant privileges privately to other administrators to manage their jobs, etc.
This is comes in handy for groups where only certain members of a group who were cross trained in an area should be responsible for a job task, EM template creation, etc.
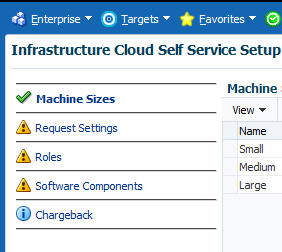
These roles can be created from Setup, Security, Roles and managed/granted via Setup,Cloud, Infrastructure.
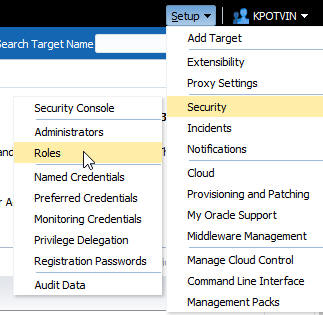
To create one, we’ll go back to our Security, Roles location:
From here, we will see a list of existing roles that are part of EM12c or added from plug-in additions and manual creation. Click on Create to start the process of creating a Private Role.
Our example private role will be created, but we’ll also go over the EM CLI command that must be issued to grant the WITH_ADMIN option, so I want to prepare you for this step and know that once you get the hang of this, you will most likely skip the GUI and go to the CLI for creating any private roles.
The role is going to allow user DSMITH to manage and view a job owned by me, KPOTVIN and then with the final EM CLI step, will allow DSMITH to grant this role to others.
We’ll start by giving our new role a clear name and description. We need to checkmark the box for Private Role to notify the system that is the intent of this role creation.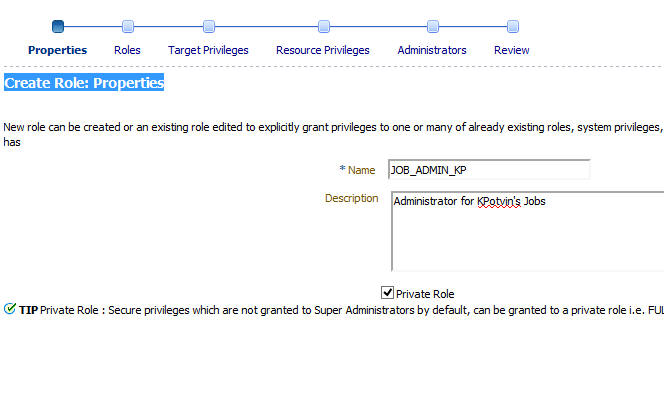
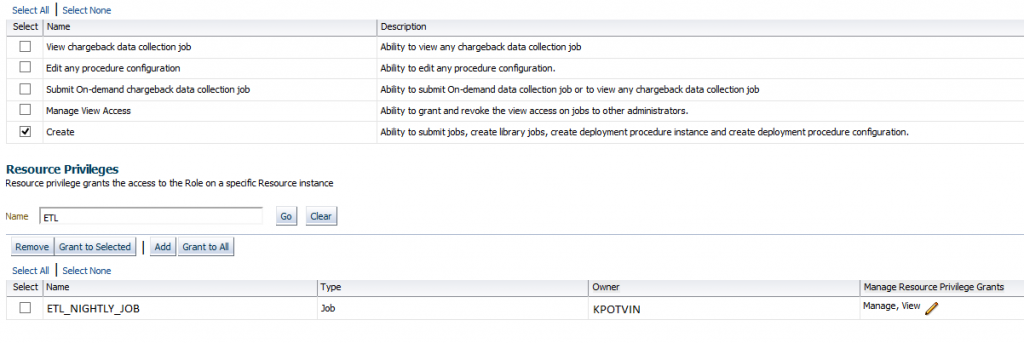
Depending the need to assign other pre-existing roles to this one, secondary grants, etc., these will be found on the next two pages, but we are onto the job system grants, found on step four of six in the wizard. We scroll down to Job System and then click on the edit option, which uses an icon of a pencil to enter the job system page.
On this page, you will see a list of options and at the bottom, I can do a search for the job that I want to allocate privileges to with this role.
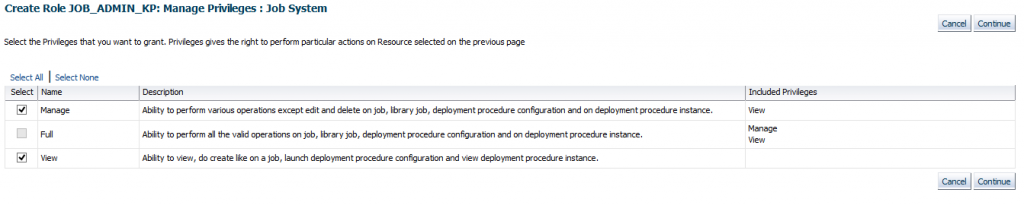
The default is to simply view the job, but if I click on the pencil in the right hand column of the job I want to allocate, I’m able to then go to the menu to add privileges:
I can then click on Continue to return me to the previous menu and if satisfied with this one job added, I can then again, click on continue to return to step 4 of 6 of the wizard:
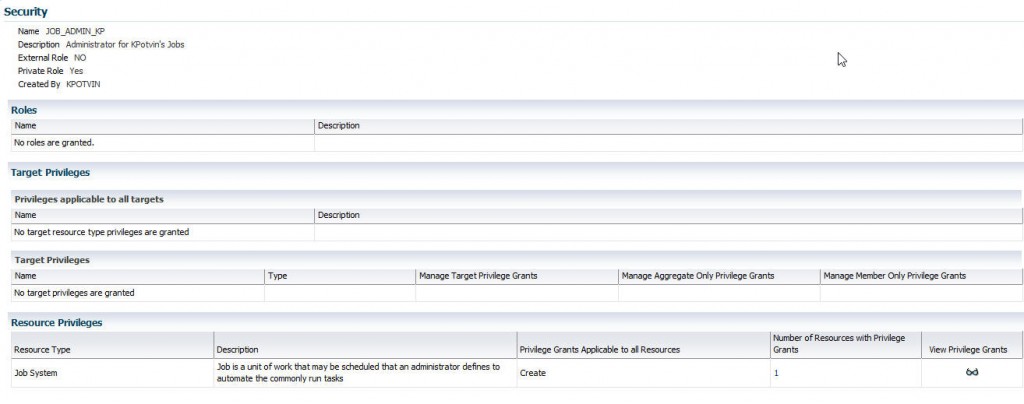
You will now see that the Job System has a value of ‘1’ for Number of Resources with Privilege Grants. Click on Continue to proceed and add the initial users you would like granted to the role.
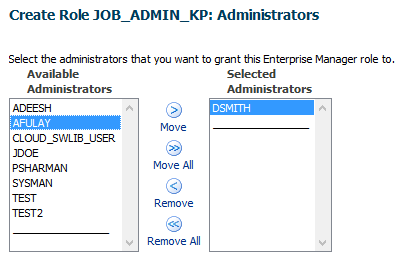
Step 5 is where we have functionality missing in the Console that must be completed at the command line interface for private roles. Click on the users that you wish to grant the new role to. Note that at the bottom, there is notification that private roles must be granted the WITH_ADMIN option from the EM CLI. Go ahead and complete who you wish to have the grant:
Now review your role and create it:
Now we need to grant with WITH_ADMIN. Just with any other role, it doesn’t harm anything to execute a grant a second time and this time, we are adding the WITH_ADMIN option.
Log into the command line interface-
>emcli login
Syncronize the CLI with the OMS:
>emcli sync
Run the grant
>emcli grant_roles -name='dsmith' -roles="JOB_ADMIN_KP" -privilege="WITH_ADMIN"
To Create the role directly from the EM CLI, the following command would complete the task:
emcli create_role -name="JOB_ADMIN_KP" -type="EM_ROLE" -desc="Role to manage KPotvin's jobs" -roles="Create_Job"-privilege="FULL_CREDENTIAL;CRED_NAME=PLB0X:CRED_OWNER=KPOTVIN" -privilege="full_job;12345678901234567890123456789012" -users="DSMITH:WITH_ADMIN" -private_role
This will create the private role and grant it to DSMITH, just as we stepped through in the console.

Pingback: EM12c Release 4, Private Roles - Oracle - Oracle - Toad World
Pingback: EM12c Release 4, Private Roles - Oracle - Oracle - Toad World
Pingback: 12.1.0.4 is HERE!! – PeteWhoDidNotTweet
Hello,
For EM 12cR4 the grant statement didn’t work for me. But following worked:
emcli grant_roles -name=’dsmith’
-roles=”JOB_ADMIN_KP:WITH_ADMIN”