EM12c Rel. 4, the Security Console
Why is the Security Console an important new feature? I was contacted by three people just this last week on how to secure an EM12c environment. How many of you are still logging in to the EM12c console or CLI with the SYSMAN account?
Bad DBA, BAD!! 🙂
Security Console
The Security Console helps the administrator set clear expectations for security standards for database administration and EM12c environment security. It provides read only dashboards that clearly show security violations and status, along with steps to secure the EM12c environment.
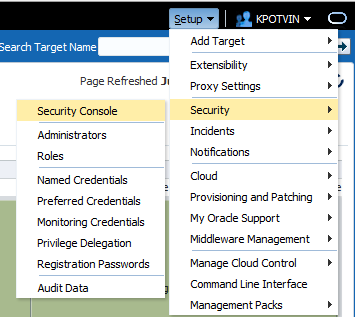
You can access the Security Console for EM12c via the Setup Menu, Security and then Security Console. Now unlike other “consoles”, the Security Console is more of a review “report” of your environment with tabs providing data breakdown and discussion of best practices for the EM12c.
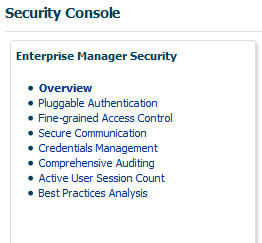
Once you get into the “Console”, it will take you through what, may for some, look like you haven’t set it up, but you are where you are supposed to be!
The left side is going to show you a menu of links that can take you through the console/report:
The Overview explains how the console works and what data you will find in each of the links below it.
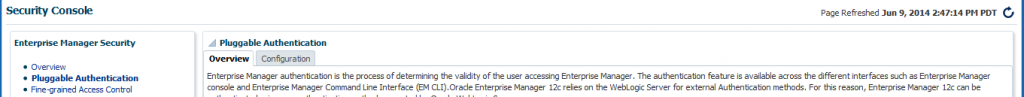
Each link has at least two tabs, one for an Overview of the section and then the results or Configuration:
Pluggable Authentication
So if we start with the first category after the Overview, the Pluggable Authentication Overview is displayed. The overview for this category will tell you about Repository-Based Authentication, (your default option for any EM12c repository) Oracle Access Manager, (ACM) which is a single sign-on method for Fusion Middleware and becoming more popular as of late, Oracle Application Single Sign-on method, Enterprise User Security Authentication, (EUS) which is an LDAP compliant Enterprise Manager solution for single sign-on and last, but not least, standard LDAP authentication through Oracle Internet Directory, (OID) or Microsoft Active Directory.
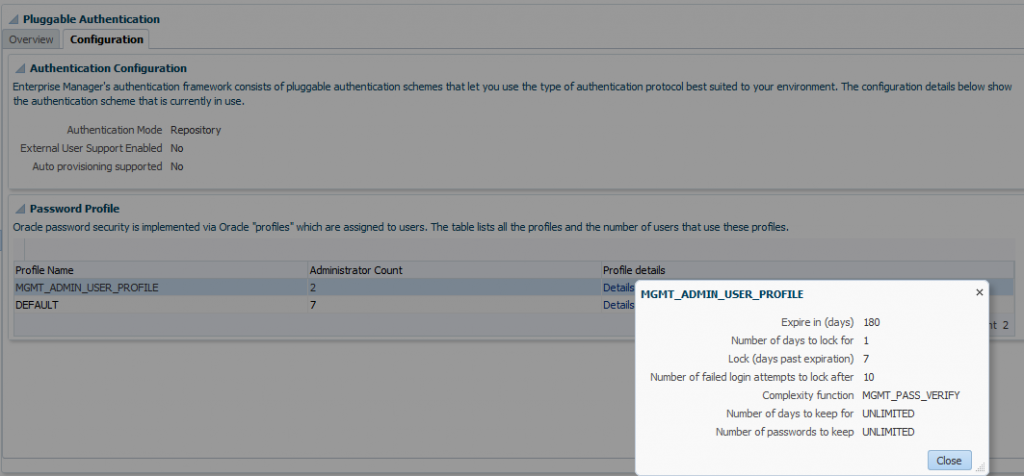
As authentication is of dire importance to your business, (it is how you are validating access to your Enterprise Manager and if not managed correctly, could inadvertently grant access to a company’s and/or customer data) knowing who has what profiles assigned to them in the EM12c environment is important, too.
The Configuration tab for Pluggable Authentication not only displays high level information about who has what profiles assigned in the repository, you can also click on the Details information to display the information about the profiles shown.
FIne-Grained Access Control
Fine-Grained Access Control has a number of tabs:
The section of the console covers information about the Repository owner, (SYSMAN) along with administrators and super administrators. It also covers privileges, roles, including out of the box and ones created to support your EM12c environment. It also provides information privilege propagation in aggregates so you can quickly assess security risks from this feature as well.
Administrators
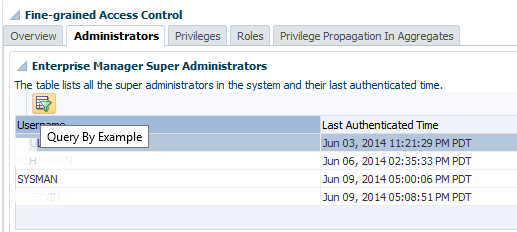
Knowing who your Super Administrators are is important and in a large EM12c environment, where you could have 100s of users, this could be a daunting task to scan lists of names looking for those with the assignment of Super Administrator
You’ll not only see a list of Super Administrators, you’ll also see the last time they logged into the repository, this could mean either the console or the EM CLI, by the way and that the SYSMAN account was logged into one today, June 9th, (bad DBA, BAD!! :))
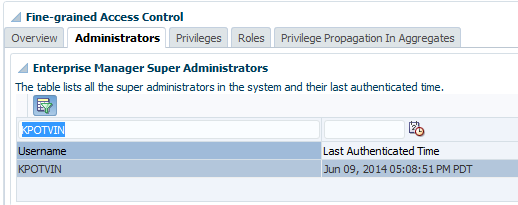
We can click on the icon at the top of the Username list, which when you hover, says, “Query by Example” and then you can do a search for either Username or Last Authenticated Time. In the example below, I can do a quick search for me in the list and it comes up promptly with the right info:
Privileges
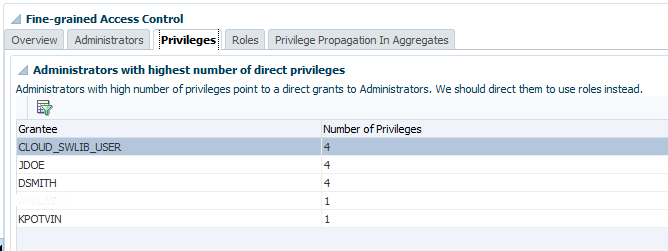
Privileges will grant us a view into who has what privileges in the repository and console. The top section of the console displays each user and quantity of privileges assigned:
There is also a note that these privileges should be considered for a role, granting them in a more efficient and secure manner.
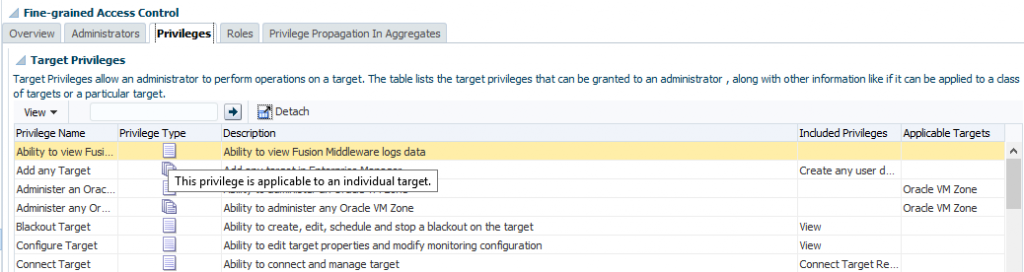
The second section focuses on Target privileges and what the privilege does. If you hover over the Privilege type, you find out if the privilege is assignable to an individual target or can be assigned to all targets of that type/class of targets.
If you’re having trouble viewing the screen and would prefer it full screen, you can click the Detach button, which will detach this section of the page and display it full screen, separate from the other aspects shown in the console.
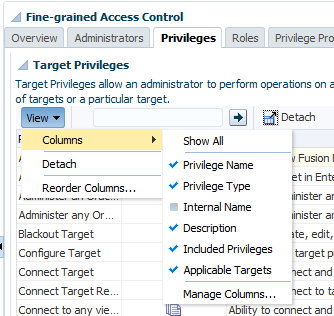
The View drop down allows you a number of options. It not only has a second opportunity to Detach the section from the screen.
From here, you can reorder or decide what columns you want to display on the screen. You can also update the columns to view what is important for you to review, (think about security audits!)
Resource Privileges
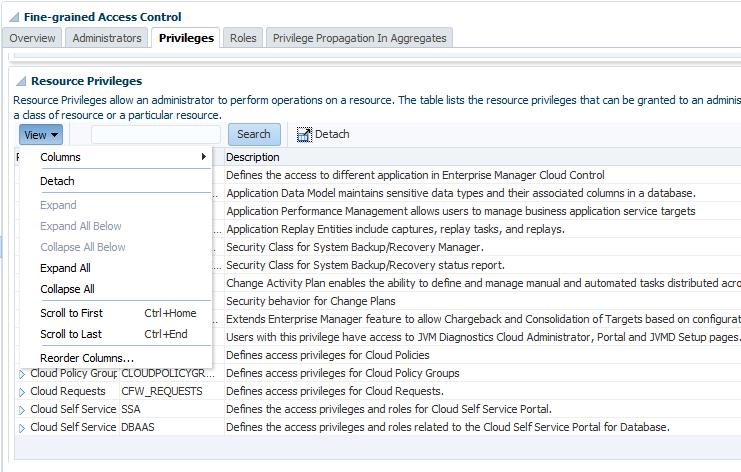
The last section is Resource Privileges and although a similar layout to Target Privileges, remember these are the privileges on WHAT you can do in the EM12c vs. what you can access and do to targets in the EM12c environment.
Notice that, just as in the previous section, we can show the internal names for privileges, (very helpful if you need to run EM CLI commands, scripts or queries.) and then you can also Expand, Collapse, order with scrolling or reorder the columns to view the data in the way that makes the most sense for what you are searching for at the time.
Roles
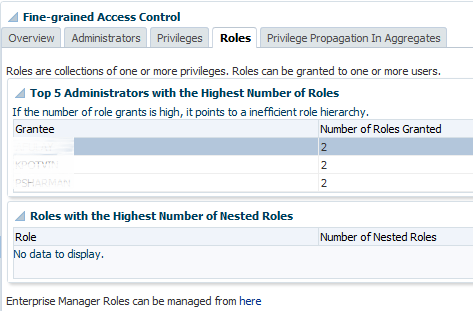
The roles section displays EM12c users and only those with roles assigned to them. Remember that being an administrator or Super Administrator is not the same as being granted a role, which this page clearly displays for you:
This section also displays Nested Role information and you can click on the link to manage roles from this page if an issue is seen.
Privilege Propagation in Aggregates
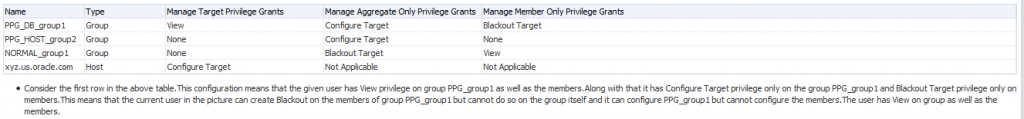
Aggregate targets have more than one member targets assigned to them, so they require a bit more special guidance to security and be a bit challenging. As this is a new feature in EM12c Release 4, the Security console can be very important to helping the administrator understand what roles are propagating what privileges to what aggregate targets. This can save from having a user with access to a member target that may not have been necessary.
The graph that is displayed at the bottom of the page shows roles that are at risk due to privilege propagation to aggregate targets, (member targets) and offers information to assist in addressing the possible threat:
Summary
All in all, the Security Console is just the first step in assisting the administrator in securing the EM12c environment that now accesses so much more than just a database. The data it provides offers great assistance to both those just starting out with Enterprise Manager as well as veterans to the product. Remember to check out this valuable new option to help secure your environment after you go to Enterprise Manager 12.1.0.4!


Pingback: EM12c Rel. 4, the Security Console - Oracle - Oracle - Toad World
Please don’t hit me with a newspaper
Pingback: 12.1.0.4 is HERE!! – PeteWhoDidNotTweet